Russian interference operations against the United States during the 2016 presidential election were vast and complex. That’s the conclusion drawn by Special Counsel Mueller, as well as by the Department of Justice, the Intelligence Community, and the Senate Select Committee on Intelligence, in the course of their respective investigations. The Russian government waged a well-documented, sustained campaign to weaken the United States, using multiple tools and tactics, damage our democracy and divide our citizens. That campaign continues today.
Acknowledging and understanding the threat is important, but only half the battle. It is up to our political leaders to act on a bipartisan basis to deter authoritarian attacks and raise the cost of waging them. The Alliance for Securing Democracy’s Policy Blueprint for Countering Authoritarian Interference in Democracies suggests a path forward to combat these threats, not only for government, but also for the other pillars of our democratic society — the private sector, including the tech companies, media organizations, and civil society organizations. We each must do our part in defending our democracy from foreign interference.
The Facts
- The U.S. Intelligence Community published a declassified joint report (ICA) assessing that Russian President Vladimir Putin ordered an influence campaign aimed at the 2016 U.S. presidential election. The ICA describes a strategy that blended covert intelligence operations with the overt efforts of the Russian government and its proxies to further polarize public and political discourse in the United States and undermine the integrity of the U.S. electoral process. The bipartisan Senate Select Committee on Intelligence’s own report on the Russian operation agreed with this assessment.
- Russian disinformation operations in 2016 targeted the political right and left, including Republican Senators Ted Cruz and Marco Rubio, Black Lives Matters activists, and secessionist movements in in Texas and California. Bottom line: Russia’s goal was to exacerbate the divisions that already exist in this country to destabilize our democracy.
- Russian social media campaigns were not executed merely by armies of bots – Russian intelligence officers actually masqueraded as Americans online.
Real Americans unknowingly participated in opposing protests that they believed were organized by fellow Americans. In fact, they were engineered over social media by Russian government operatives thousands of miles away. - Russian government activity, including disinformation campaigns, supported by state-run media and sophisticated social media efforts, continued long after election day 2016. In fact, the Department of Justice’s October 2018 indictment of the accountant for the Russian government-sponsored Internet Research Agency (IRA) showed that the IRA’s budget increased 70% between 2016 and 2018. This demonstrates that authoritarian interference does not begin and end with any particular election. It is an ongoing challenge.
- Operatives from Russia’s military intelligence agency (GRU) hacked into the systems of the Democratic National Committee and the email accounts of top Clinton campaign officials, stole private emails and released those emails publicly through three channels: GRU-operated DCLeaks, Guccifer 2.0 and WikiLeaks.
- The Department of Homeland Security (DHS) stated that Russian government hackers targeted the election infrastructure of 21 U.S. states ahead of the 2016 election, successfully penetrating a small number of them.
- Russia’s tactics are more expansive than just cyberattacks and disinformation campaigns. Russian national Maria Butina was indicted for operating as a foreign agent to establish a “back channel” with U.S. politicians, highlighting the wide range of Russian tactics and the ongoing nature of these operations.
- GRU officers continued cyberattacks on U.S. entities well into 2018. An October 2018 DOJ indictment stated that from December 2014 until at least May 2018, Russian military intelligence officers “conducted persistent and sophisticated computer intrusions affecting U.S. persons, corporate entities, international organizations, and their respective employees located around the world, based on their strategic interest to the Russian government.”
“I know what they [the Russian government] did in ’16. I know what they tried to do in ’18. What will they do in 2020? That’s what keeps me up at night.” — Chris Krebs, Director of the Cybersecurity and Infrastructure Security Agency (CISA), March 13, 2019
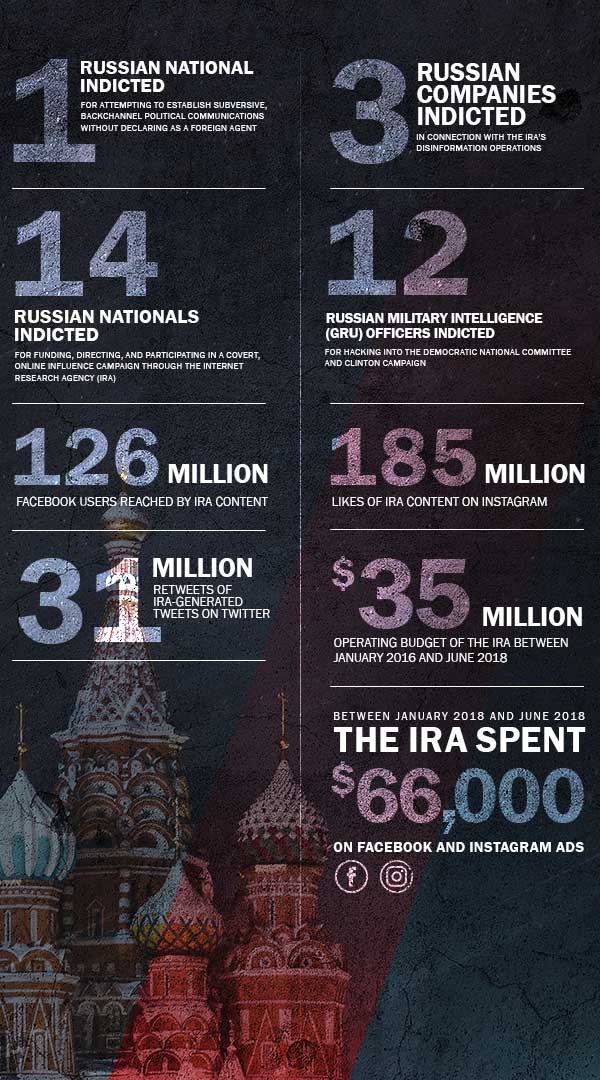
Russian interference by the numbers